Evaluate your cybersecurity posture to identify vulnerabilities
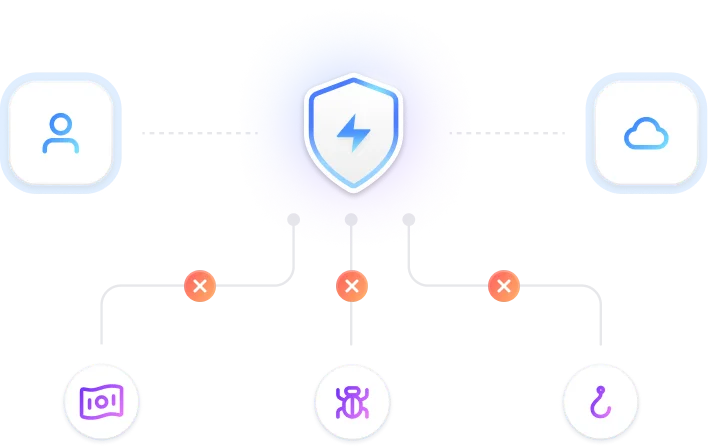
Defend Your Business from Cyber Threats
Protect your organization with our cutting-edge cybersecurity solutions designed to prevent data breaches and ensure business continuity.
Solutions for every security goal
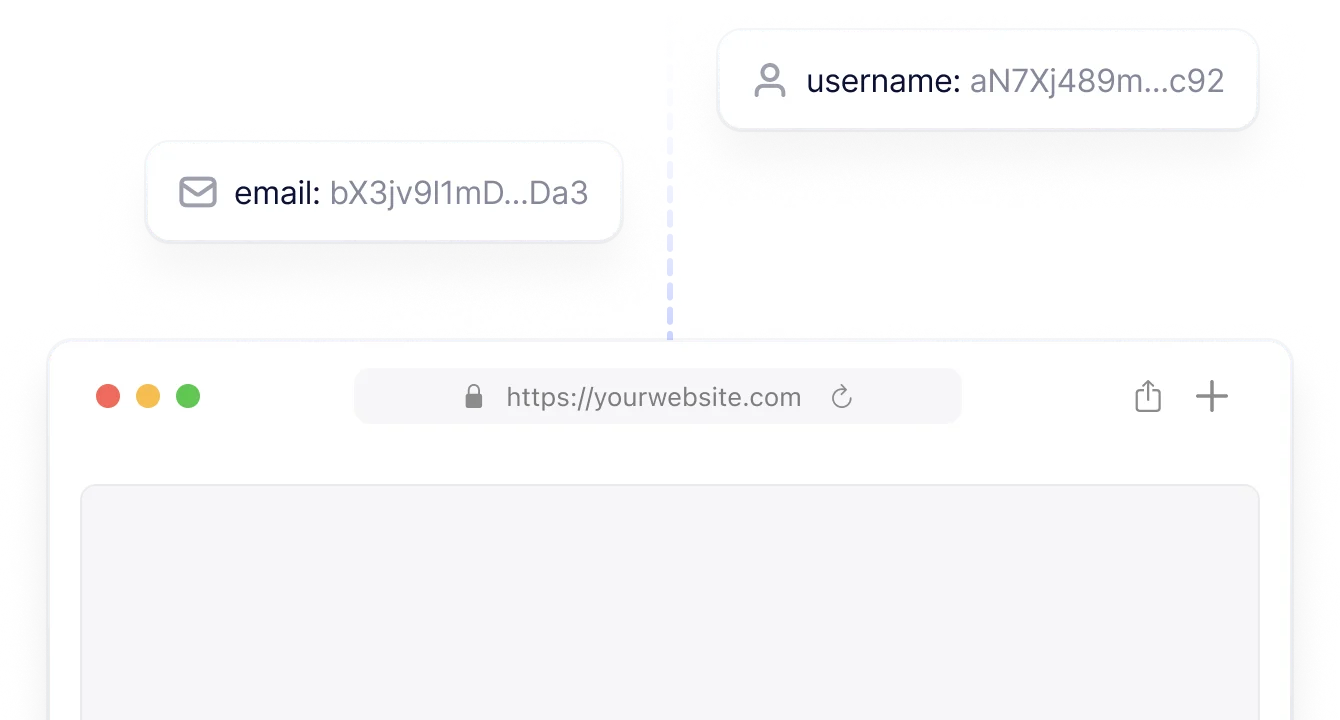
Data Encryption Services
Ensure that sensitive data remains secure with state-of-the-art encryption methods that protect information both at rest and in transit.
Threat Analysis
Identify and neutralize cyber threats in real-time with our advanced detection systems, protecting your business from potential breaches.
Incident Response and Recovery
Minimize damage from cyber attacks with rapid response protocols and recovery solutions to restore normal operations swiftly.
Security Audits and Assessments
Regularly review and evaluate your cybersecurity posture to identify vulnerabilities and enhance defenses
Penetration Testing Services
Simulate real-world cyber attacks to identify weaknesses in your defenses and reinforce your security measures before breaches occur.
Regulatory Solutions
Stay ahead of industry standards with compliance tools and processes that align with GDPR, HIPAA, and other regulations.
Rapid Incident Response and Recovery
Minimize downtime and recover swiftly from cyber incidents with our expert response teams and disaster recovery plans.
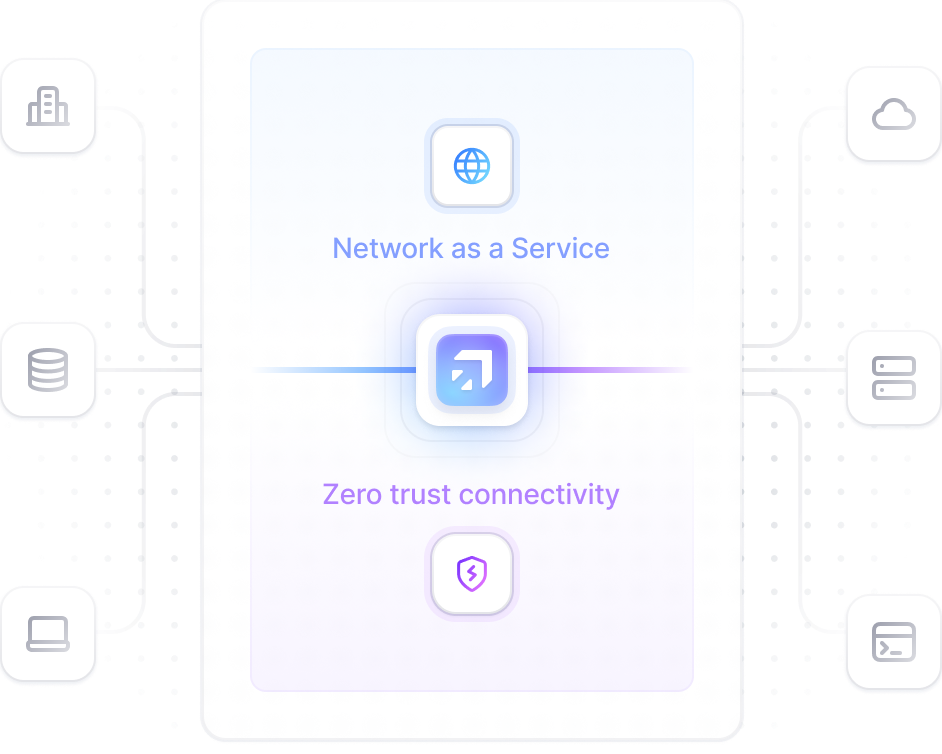
Secure Your Digital Infrastructure
Fortify your network and digital assets with top-tier firewalls, encryption, and secure access controls.



Data Protection
Advanced Threat Detection Systems
Stay one step ahead of cybercriminals with real-time threat monitoring and rapid response protocols tailored to your business.

Comprehensive Cloud Security
Safeguard your cloud-based data and services with robust protection designed to prevent unauthorized access and breaches.
Frequently Asked Questions
Got any questions? we’re here to help
What is cybersecurity and why is it important?
Our advanced threat detection identifies malicious activities in real-time and responds swiftly to neutralize risks before they cause damage.
Without cybersecurity, businesses risk data breaches, financial losses, reputational damage, and regulatory penalties.
We provide robust cloud security solutions, including encryption, access control, and real-time monitoring to ensure your cloud data is protected.
Regular security audits are recommended at least annually, or more frequently for high-risk industries, to identify vulnerabilities and improve defenses.
Our incident response includes threat containment, data recovery, root cause analysis, and preventive measures to reduce future risks.